On July 18th, Singapore’s National Security Minister K. Shanmugam reported that the country’s infrastructure was attacked by a “highly sophisticated threat actor”. Google’s cybersecurity firm Mandiant later identified the espionage group, UNC3886. Intel has linked connections of their latest strike to China, which the Chinese Embassy of Singapore refused to accept on July 21st.
Who is UNC 3886?
Mandiant first discovered UNC3886 when they targeted cloud and virtualization software company, VMware, in 2022. The cyberattackers exploited their ESXi hypervisor program by developing and planting spyware. Researchers analyzed their malicious boot profile and discovered a dangerous technique involving vSphere Installation Bundles (VIBs).
Their programming created a series of backdoors that allows UNC3886 to infiltrate VMware’s administration access under falsified acceptance levels. The disguised spyware then scans and steals user data. Mandiant found the espionage group’s firmware store with files under the names VirtualPITA, VirtualPIE, and VirtualGATE. By using various coding and encryption techniques, these files will harvest user credentials to bypass their target’s antivirus software.
Utilizing the Zero-Day Exploit to Create Sneaky Malware
UNC3886’s cyberattacks continued throughout 2023 and 2024. Mandiant watched as the hackers perfected the zero-day exploit. IBM describes the company’s malware method as an unknown signature that remains undetectable by credential-based threat detectors. Once it infiltrates an organization’s cybersecurity, technicians are left with no time to react and search for a solution. Since 1988, zero-day exploits have taken days, months, or years to find traces of cybercriminal activity.
During January 2023, Security Affairs reported that Fortinet’s FortiOS suffered an SSL-VPN zero-day exploit. UNC3886 executed a malware patch under CVE-2022-42475. Fortune 500’s Resecurity discovered that the file was earlier marketed privately through underground brokers on the Dark Web. OpenText found the same vulnerabilities in their enterprise content management (ECM) system under multiple patches labeled CVE-2022. This cyberattack began back in October 2022.
Mandiant collaborated with UNC3886-affected companies to research their infiltration pattern. In a 2024 Google Cloud blog, the cybersecurity firm released a full visual guide to alert the public. Unfortunately, it was released after misled users downloaded the CVE-2023 patches. Tech companies quickly developed debugging guides to restore their operating systems.
Singapore’s 4th Cyberattack

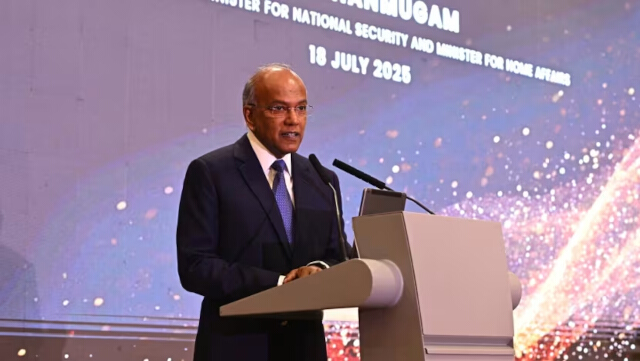
National Security Minister Shanmugam spoke about UNC3886’s latest cyberattack while celebrating Singapore’s 10th anniversary of their Cyber Security Agency. The nation is the 4th advanced tech leader in the world, making it a higher target for cybercriminals.
In 2018, Singapore’s largest health provider, SingHealth, had their IT systems hacked. Prime Minister Lee Hsien Loong told the press that 1.5 million patients had their data breached. Over 160,000 had their outpatient medication stolen. Health Minister Gan Kim Young sincerely apologized to citizens for suffering through the country’s worst cyberattack.
CSA Chief Executive David Koh commented at the time:
“This was a deliberate, targeted, and well-planned cyber attack. It was not the work of casual hackers or criminal gangs.”
According to Central NewsAsia, Shanmugam and the CSA have been monitoring UNC3886’s activities. With Singapore’s 4th cyberattack, they are determined to study and counter their advanced persistent threats (APTs). The CSA has disclosed further information on which sectors in their infrastructure have been hacked.
Shanmugam told Singaporeans how dangerous UNC3886 is:
“[These hackers have been associated] with cyberattacks against critical areas, including defense, telecommunications, and technology organizations in the US and Asia. The intent of this threat actor in attacking Singapore is quite clear. [UNC3886] is going after vital infrastructures that deliver essential services. If these [APTs] succeed, they will conduct espionage and cause major disruption [within our nation].”
However, the situation has escalated to questioning UNC3886’s origin of operation. Mandiant has traced the VMware incident to Beijing, China. They came to this conclusion again on March 11, 2025. This time, cybersecurity officials found the virus integrated within Juniper Networks’ JunoOS routers. They traced their connections back to the same location.
The Chinese Embassy in Singapore viewed the firm’s reports as “unwarranted smearing”. Beijing representatives deny these allegations as they oppose any form of cyberattacks.